
File Access Control for Mac
See when apps reach for files you didn't mean to share.
macOS endpoint security — file access monitoring and control
Vedette shows you when software reaches for SSH keys, .env files, wallet data, cloud credentials, contracts, and financial records. Then you can lock that access down with narrow rules tied to the apps you trust.
~/.ssh
.env*
~/.aws/credentials
Wallet files
Sensitive documents
Annual subscription: $59.99/year. Includes a 7-day trial. Card required.
Manage subscription
Why people buy Vedette
People buy Vedette when they realize a few folders on their Mac are too important to leave open to every app.
Protect developer secrets
Keep IDE extensions, package scripts, helpers, and local agents away from ~/.ssh, .env*, ~/.aws/credentials, and ~/.kube/config.
Protect wallet and finance files
Keep apps away from wallet directories, exported keys, account statements, tax records, and other files that can cost you money fast.
Protect sensitive documents
Lock down contracts, customer exports, research folders, legal files, and personal records instead of giving every app broad access to your home directory.
Why this matters now
These incidents are different, but they point to the same thing: once software can read a file on your Mac, it can leak it.
March 24, 2026
LiteLLM compromise
The malicious PyPI releases 1.82.7 and 1.82.8 harvested local secrets from infected machines, including SSH keys, .env files, cloud credentials, Kubernetes configs, shell history, and wallet files.
Agentic file access
Prompt injection remains an agent risk
OpenAI's Operator system card says prompt injection remains an area of concern, and its March 11, 2025 API update notes that a successful prompt injection can have higher impact on Local OS in non-browser environments.
July 17, 2025
Personal wallet compromises are growing
Chainalysis reported that personal wallet compromises made up 23.35% of all stolen fund activity year-to-date in 2025, reflecting a growing share of total ecosystem theft.
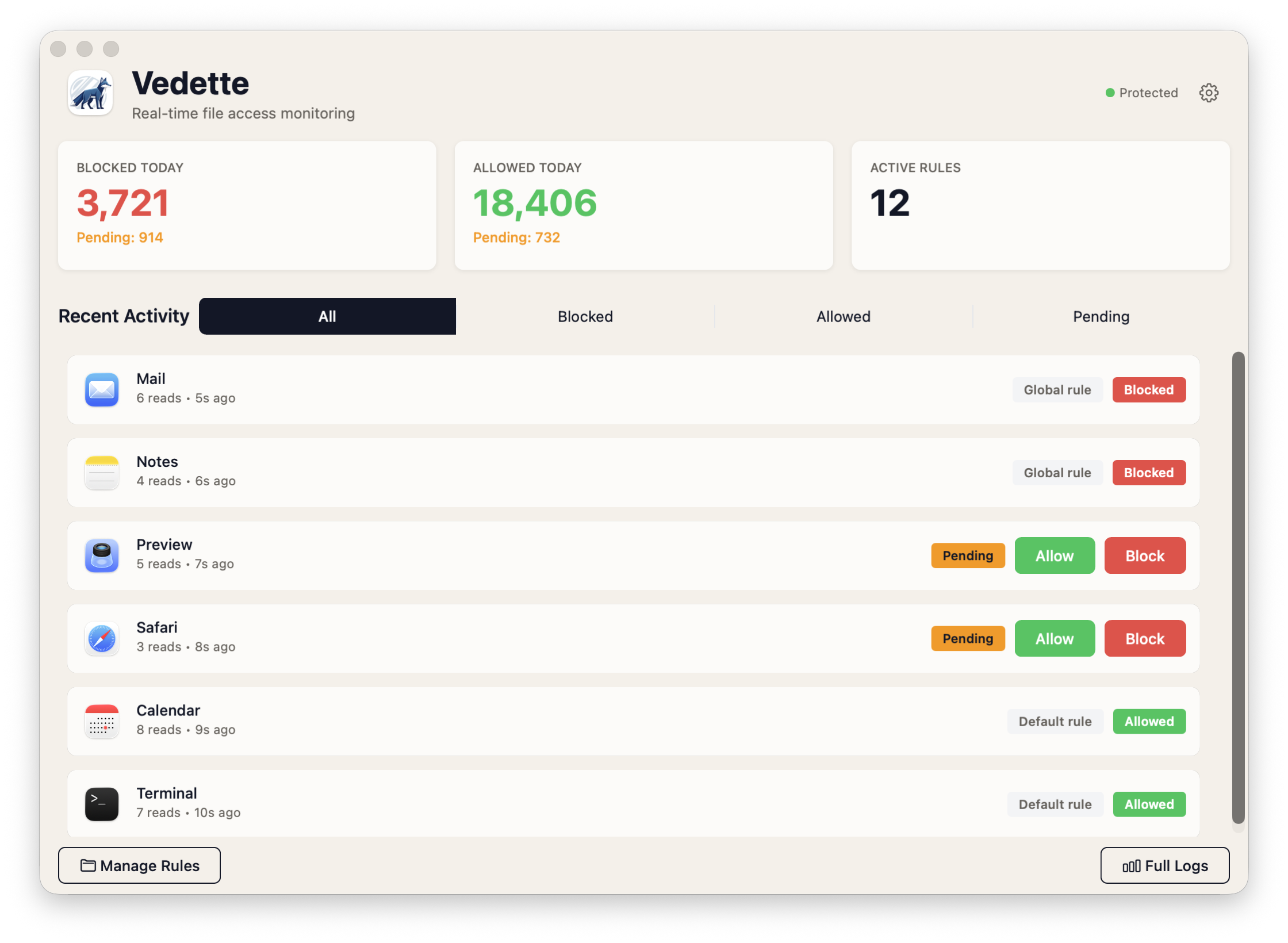
How Vedette protects
Vedette does not stop every access with a popup. It enforces from rules, records what happened, and gives you a way to tighten things up after the fact.
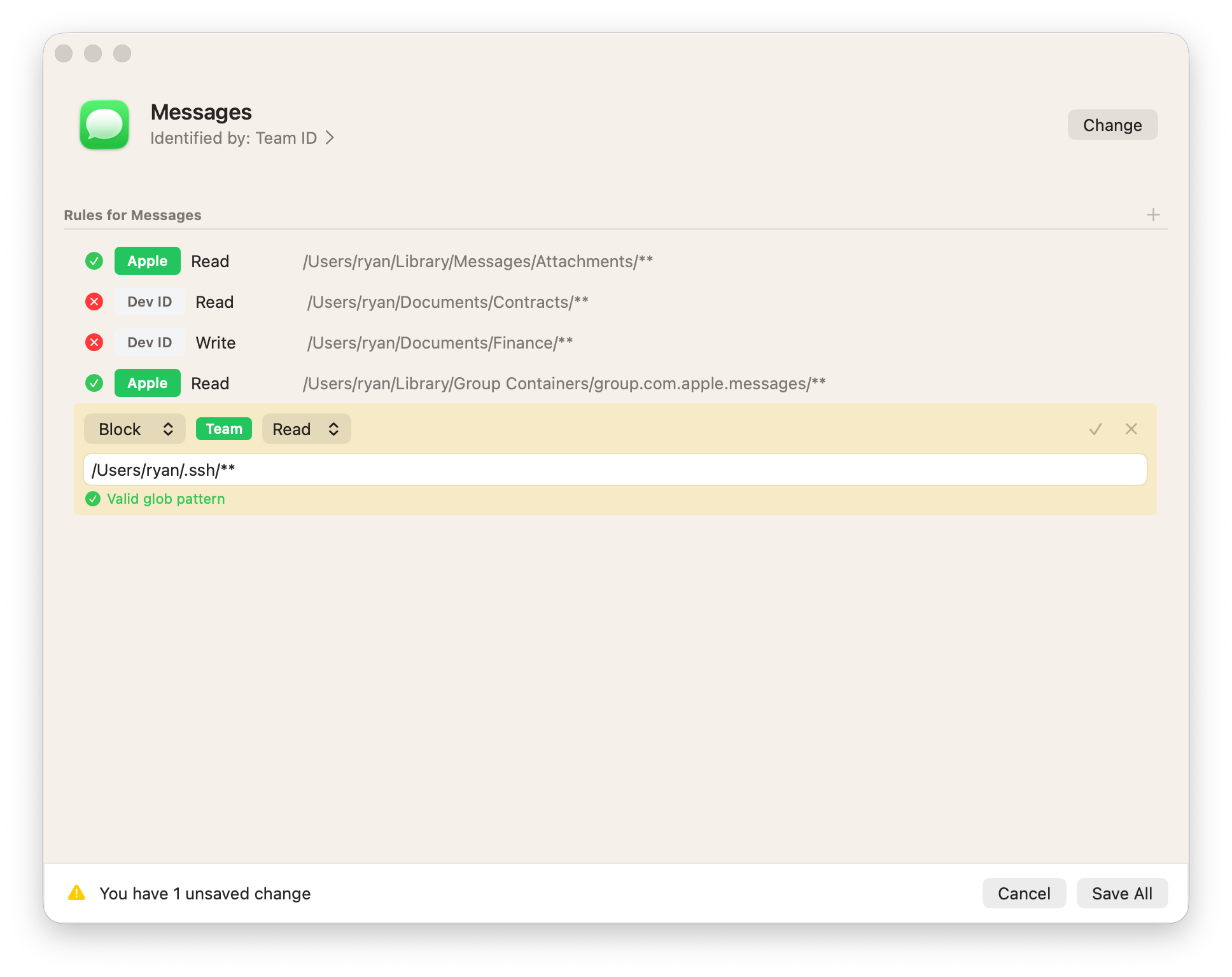
Rules tied to app identity
Bind rules to stable app identity like Team ID, Signing ID, certificate hash, or a path fallback instead of trusting only a process name.
Path and operation scoping
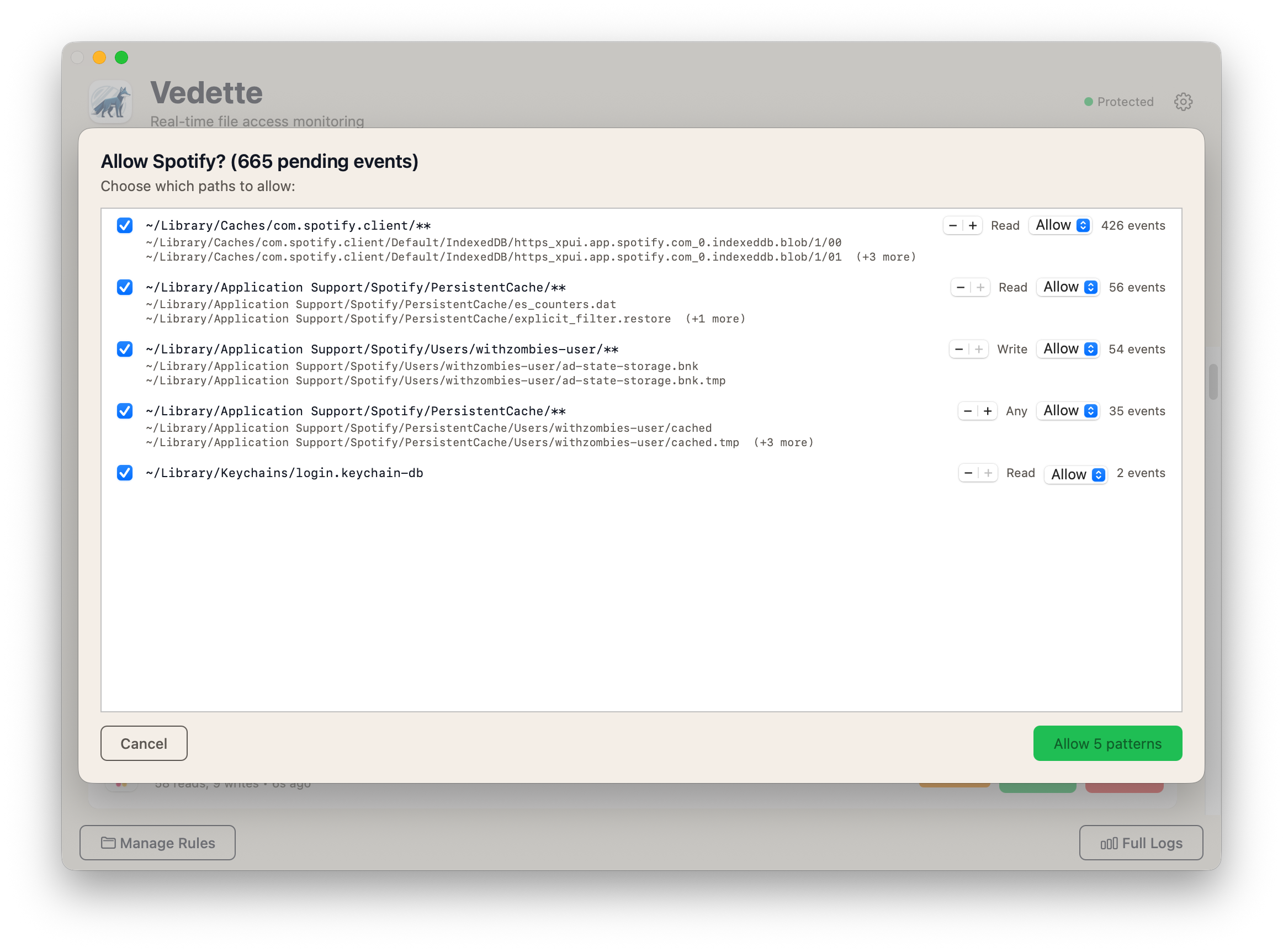
Allow or block exact paths, globs, or broader patterns and scope decisions to read, write, or all access depending on the file boundary you want.
Trust-aware rules
Differentiate between Apple-signed, Developer ID, ad-hoc signed, or unsigned software so your rules can reflect how much trust you want to extend.
Reviewable activity and rules that stick
See what a process touched, spot recurring patterns, and turn that into rules so you do not have to answer the same question over and over.
Vedette in action
You look at what happened, inspect the process, and write the narrowest rule that still gets your work done.
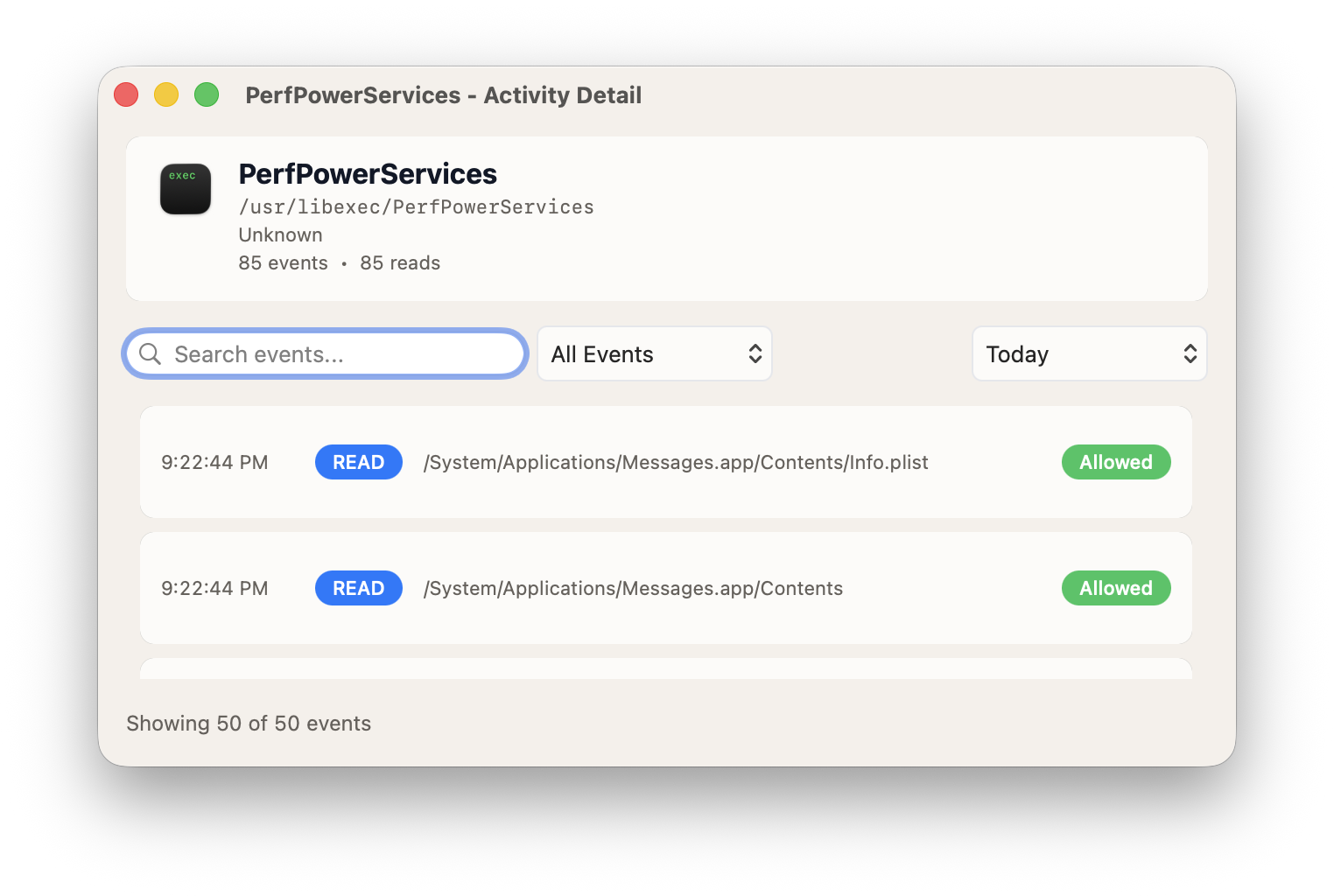
Process-level forensics
Open one process and see exactly what it tried to read or write before deciding what to allow next time.
Precise rule creation
Turn reviewed access into path rules tied to the identity you trust, instead of granting a broad exception and forgetting about it.
Fast review when something new shows up
When Vedette finds a new pattern, review it once, decide how wide the rule should be, and move on.
Setup and trust model
Vedette is native macOS security software. You approve the extension, grant Full Disk Access, and it enforces from local rules on the machine.
Platform
macOS 14+
Approval
System extension approval
Permission
Full Disk Access
Enforcement
Local rules, reviewable activity
Get Vedette
Install the app, complete checkout, and activate your license in the app.
Annual subscription
$59.99/year
Includes a 7-day trial. Card required. Cancel within 7 days to avoid annual billing.
Buy Vedette Download Vedette Manage subscriptionFrom Aquilon Security
Need endpoint DLP for your team?
Detect PII, credentials, and compliance violations across your fleet.